TECHNICAL SHEET
1.GENERAL INFORMATION ABOUT THE INVENTION
1.1 Title of invention
PUBLIC KEY AUTHENTICATION METHOD
1.2 Subject area
INFORMATION SECURITY
2.PARTICIPANT INFORMATION
FULL NAME: JONATHAN FRANCHESCO TORRES BACA
AGE: 28
PHONE NUMBER: 051 958429349
EMAIL: Chescot2302@gmail.com
IDE: 45329234
ADDRESS: Av. Gran Chimu 1264
COUNTRY: Peru
REGION: Lambayeque
PROFESSION: Software Developer
3. TECHNICAL DETAIL
3.1 Technical background
Patent:
US 2013/0246796 A1
Title:
SYSTEM AND METHOD FOR SECURING DATABASE ACTIVITY.
Inventors:
Aviad Lichtenstadt, Tel Aviv (IL); Guy
Lichtman, HertZliya (IL); Slavik
Markovich, Los Altos, CA (US)
Assignee:
McAfee, Inc.
Publication date:
Sep. 19, 2013
Abstract:
A method is provided in one example embodiment that includes detecting database activity associated with a statement having a signature, validating the signature; and evaluating the statement as a signed statement if the signature is valid. In more particular embodiments, the signature may include a unique script identifier and a hash function of a shared key. In yet other embodiments, validating the signature may include checking a session variable and comparing the statement to a list of signed statements.
A method is provided in one example embodiment that includes detecting database activity associated with a statement having a signature, validating the signature; and evaluating the statement as a signed statement if the signature is valid. In more particular embodiments, the signature may include a unique script identifier and a hash function of a shared key. In yet other embodiments, validating the signature may include checking a session variable and comparing the statement to a list of signed statements.
Technical field
This specification relates in general to information systems, and more particularly, to a system and method for securing database activity. Background Databases and their database management system (DBMS) counterparts have evolved to facilitate designing, building, and maintaining complex information systems, but databases and DBMSs themselves have also evolved into quite complex systems. The size, capabilities, and performance of databases and DBMSs have grown by orders of magnitude along with the progress of technology in the areas of processors, computer memory, computer storage, and computer networks.
Databases often contain sensitive data, which usually resides within tables that can be used by various applications. Many types of controls can be implemented to protect databases (and the sensitive data within them). For example, network security measures may be used to guard against unauthorized external access, while database activity monitoring tools can be used to audit internal activity and guard against authorized access for unauthorized purposes. However, these controls may not be able to differentiate adequately between authorized and unauthorized access to sensitive data by an authorized user. A manual investigation is often necessary to determine if many activities are approved. Thus, significant challenges remain for designing and implementing systems and methods for
securing database activity.
3.2 Difference between proposed innovation and background
The public key authentication method or GO method is designed to safeguard the connectivity data to the storing services, meanwhile it allows controlling and monitoring the users’ authentication in 3 levels, which means there is a system user for each database user, thus GO method guarantees the monitoring of SQL activities for each one authenticated user. Unlike to the background, GO method does not sign the running sentences, but when the systems and storing services validated the user credentials, GO method stores the object connectivity within the RAM memory in a list key - value. The key is a plain text called public key which is encrypted by any encrypting algorithm and the value is the objectconnectivity that allows communication between the applications and the storing services.
As it was mentioned above the Go method is based in a 3 levels authentication, the higher and riskier level is denominated "SUPERGOADMIN" authentication, the users who want to be authenticated at this level must provide connectivity data to storage services and the public key, which is encrypted and is also the key to store the object connectivity in a key - value list. The middle level is denominated “GOADMIN" authentication, the users who want to be authenticated at this level must provide a logic user name and a key, the database schema to which will be connected and a public key in addition to the public key generated by the “SUPERGOADMIN" authentication, this SUPERGOADMIN's key is essential in this process, inasmuch as "SUPERGOADMIN" users authenticate to the "GOADMIN" users. The last level is denominated "GOUSER", this is end users authentication, in this level the users must provide a logic user name and a key, a non-repudiation key and the public key generated by the “GOADMIN" authentication.
In summary, "SUPERGOADMIN" allows to authenticate “GOADMIN" users and “GOADMIN" allows to authenticate "GOUSER" users. The main objective of this method is safeguard the connectivity data and also serve as a user’s authentication method, its implementation’s benefits are:
- Allows to develop a DAM (Database activity monitor), which can control and monitor the system and database users’ SQL activities.
- Allows to management the load balancing.
- Allows a dynamic storing service both physically and logically. It means that no matter neither the logical location (network level) nor physical location (geolocation) of the storing service.
- Allows to develop a strategy of licenses for applications SAAS type.
3.3 Technical advantages
- Safeguard the connectivity data, because these neither are stored on a plain text nor are embedded in the source code, in addition these are destroyed once obtained the object connectivity.
- High performance, since the object connectivity is stored on the application server’s RAM memory in one client - server architecture, improving in this way the connectivity time with the storing services.
- Control the number of connections and open sessions. Allows to develop a DAM (Database activity monitor), which can control and monitor the system and database users’ SQL activities.
- Allows a dynamic storing service both physically and logically. It means that no matter neither the logical location (network level) nor physical location (geolocation) of the storing service.
- Allows to management the load balancing.
3.4 Invention Description
GO AUTHENTICATION METHOD OR PUBLIC KEY AUTHENTICATION METHOD
I.- ABSTRACT
It is a method which safeguards the connectivity data to the storing services, allowing developers to connect their applications without worrying about exposing the data in physical files or embedding the connectivity data within the source code. It also provides a user authentication model in 3 levels, it is a solution ideally suited to corporative groups which manage big business units, due to the centralization of users' information, allowing to control and monitor the users' SQL activities.
II.- OBJECTS
- Protect the connectivity data to storing services
- Provide a user authentication model in 3 levels
- Monitor the users’ SQL activities
- Centralize users’ information
- Allow to management the load balancing
- Assure the users' non-repudiation
1. SUPERGOADMIN USER
This user authenticates at database level. It allows the "GOADMIN" user authentication by using a public key generated by "SUPERGOADMIN" at the authentication time, this is why "SUPERGOADMIN” must be authenticated before all the other users. This user has a data store named in the same way,where the users' information is stored (GOADMIN and GOUSER), allowing a centralized administration of the users and their credentials.
2. GOADMIN USER
This user authenticates its credentials at system level and database level, the system credentials are compared within user table of SUPERGOADMIN database, with objective of exchanging this data by connectivity data to the GOADMIN database. It allows the GOUSER authentication using public key generated by GOADMIN, that's why GOADMIN must be authenticated before GOUSER. The GOADMIN database contains user credentials GOUSER, which enable to perform DML operations over the tables related to the
company business rules, it can be said that a GOADMIN database is a business database.
3. GOUSER USER
This user authenticates its credentials at system level and database level, the system credentials are compared within user table of GOADMIN database, with objective of exchanging this data by connectivity data to the GOADMIN database. The GOUSER users are considered as end users of the information system, they are not a database owner since they have reading and writing privileges over GOADMIN database's objects
4. Connectivity data
These data are used by developers to connect their application to a certain database e.g., MySQL, Postgres, Oracle, etc.
5. Private Key
This key must be kept secret by the assigned users to avoid unauthorized access to their accounts or log on to the system.
6. Public key
This key is provided from a user with higher hierarchy to others authorized users in order to allow them to use its session or connection to the database to authenticate themselves to the system.
7. Non-repudiation key
It enables to identify the user’s connections and make a manual inspection when there is an anomaly related to double access to the system from many network points. The manual procedure is to ask to the authorized user his/her non - repudiation key, thus identifying the abnormal connection and taking appropriate actions.
Devices which allows to connect to network LAN or WLAN, most popular devices to manipulate information systems are laptops, smartphones, tablets, etc.
9. Data Input Interface
It allows input and output data.
10. Encryption algorithm
Allows to encrypt information in order to keep it safe from unauthorized users.
11. RAM
It allows to store data and programs which are run over the operating systems.
12. Key Value lists
They are array nx2, n rows and 2 columns. In the First column is the key and in the second the value, so that it only can access the value by the key.
13. Database
Structure which enable persist data over time
IV.- DESCRIPTION
GO AUTHENTICATION METHOD allows to the developers to create information systems without the risk of exposing connectivity data (D1) to the databases (B1, B2 and B3), as well as end users authentication (U3). This method sends the connectivity data to the server via an interface, once the connectivity data is verified the connection to the database is opened, all the connection are stored on server's RAM (R1) on a key value list.
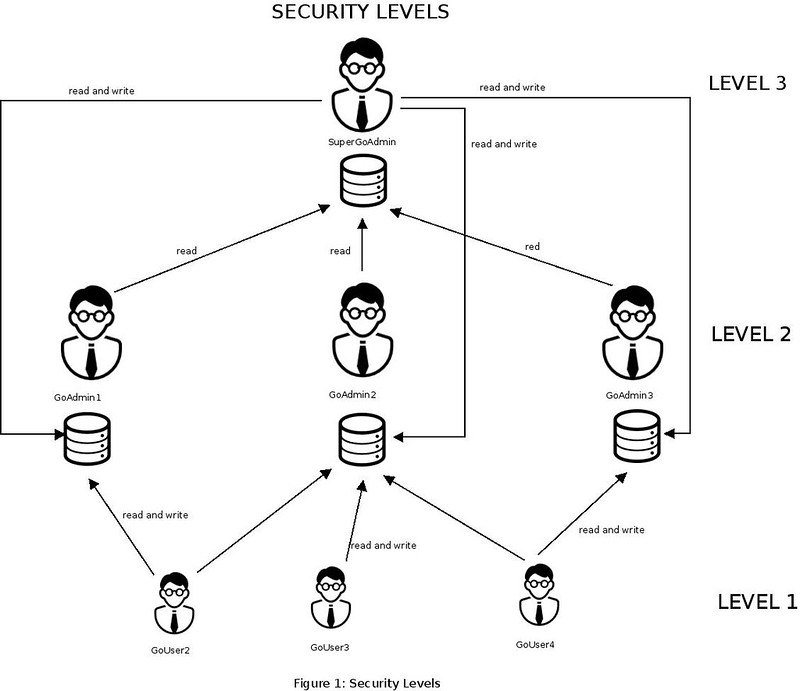
Figure 1 shows the three security levels of this method, which begins from the highest and riskiest level, this is why it is recommended to make the authentication in a safe environment and if possible from the application server itself (server which host our application running).
Figure also shows that GOUSER users (U3) do not own any database, so there is no necessary to have a user of database for each one of them, thus reducing the connections number to the database server, only in case it was necessary to monitor the SQL activities of the GOUSER user, the user (U3) must beassigned a user database.
SUPERGOADMIN user Authentication(Zoom in)
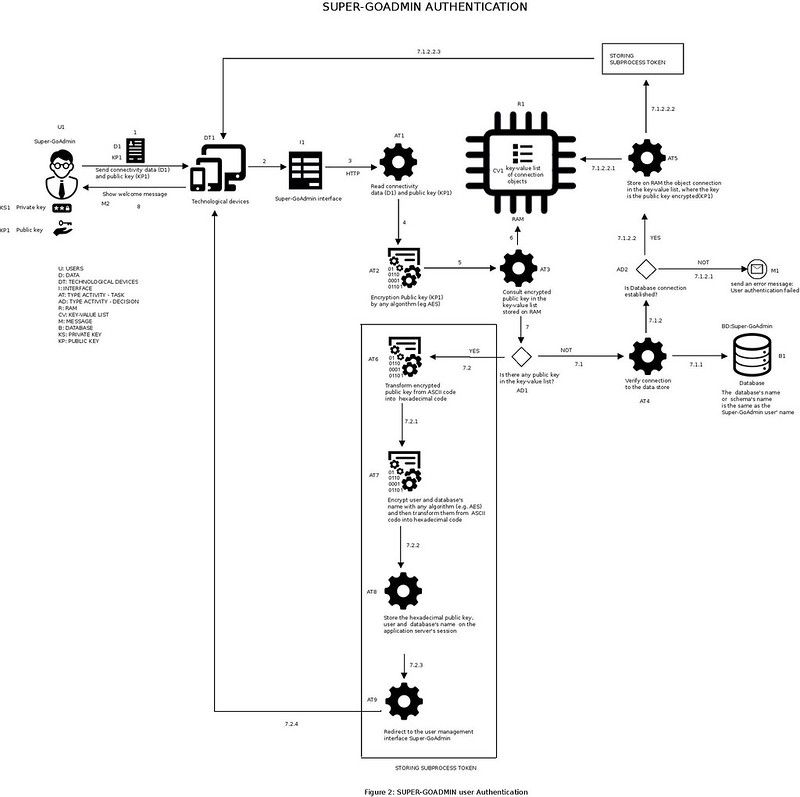
Figure 2 shows through a flow diagram, how the SUPERGOADMIN user (U1) is authenticated and opens a connection to database.
The user U1 sends the connectivity data (D1), these data contains the private key (KS1), to the database (B1) and the public key (KP1), through technological devices (DT1), which are connected to a network LAN or WAN, communicates with the application server, that contains the computing system which implements the GO AUTHENTICATION METHOD, this communication is done by an interface (I1), this interface allows to send the data (D1 and KP1), using the HTTP protocol, to application server, where the connectivity data (D1) are read, the public key (KP1) is encrypted, the next step is to consult the encrypted public key in a key value list, which is stored on application server's RAM (R1).
If the encrypted key is already in the key value list, it means the user (U1) was authenticated previously, in order to keep the integrity throughout of the transmission from the client to the server, the encrypted key is transformed from ASCII code into hexadecimal code. Part of the connectivity data are the user and database's name, they are encrypted and transformed as was previously the KP1. The KP1, the user and database's name are stored on the application server's session and the user (U1) is redirected to
SUPERGOADMIN’S administration interface, giving a welcome greeting (M2).
If the encrypted key is not in the key value list (CV1), which is stored on application server's RAM (R1), then the connectivity to the database is checked using the connectivity data (D1), which were previously read, and the persistence technology , according to the used language, as JDBC, JPA and JDO, if there is no connection to Super-GoAdmin database (B1) an error message (M1) is sent and shown through an interface, but if the connection is correct, the object connectivity is stored in the key value list (CV1), this
object connectivity can only be obtained through an encrypted public key and. Afterward the process of storing the token on the application server is run.
GOADMIN user Authentication(Zoom in)
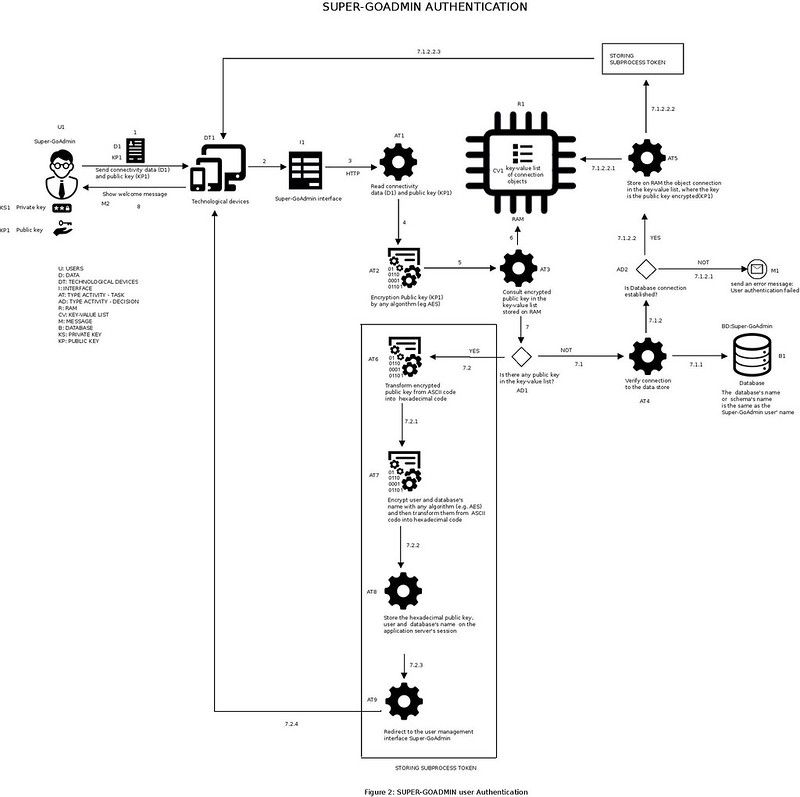
Figure 2 shows through a flow diagram, how the SUPERGOADMIN user (U1) is authenticated and opens a connection to database.
The user U1 sends the connectivity data (D1), these data contains the private key (KS1), to the database (B1) and the public key (KP1), through technological devices (DT1), which are connected to a network LAN or WAN, communicates with the application server, that contains the computing system which implements the GO AUTHENTICATION METHOD, this communication is done by an interface (I1), this interface allows to send the data (D1 and KP1), using the HTTP protocol, to application server, where the connectivity data (D1) are read, the public key (KP1) is encrypted, the next step is to consult the encrypted public key in a key value list, which is stored on application server's RAM (R1).
If the encrypted key is already in the key value list, it means the user (U1) was authenticated previously, in order to keep the integrity throughout of the transmission from the client to the server, the encrypted key is transformed from ASCII code into hexadecimal code. Part of the connectivity data are the user and database's name, they are encrypted and transformed as was previously the KP1. The KP1, the user and database's name are stored on the application server's session and the user (U1) is redirected to
SUPERGOADMIN’S administration interface, giving a welcome greeting (M2).
If the encrypted key is not in the key value list (CV1), which is stored on application server's RAM (R1), then the connectivity to the database is checked using the connectivity data (D1), which were previously read, and the persistence technology , according to the used language, as JDBC, JPA and JDO, if there is no connection to Super-GoAdmin database (B1) an error message (M1) is sent and shown through an interface, but if the connection is correct, the object connectivity is stored in the key value list (CV1), this
object connectivity can only be obtained through an encrypted public key and. Afterward the process of storing the token on the application server is run.
GOADMIN user Authentication(Zoom in)
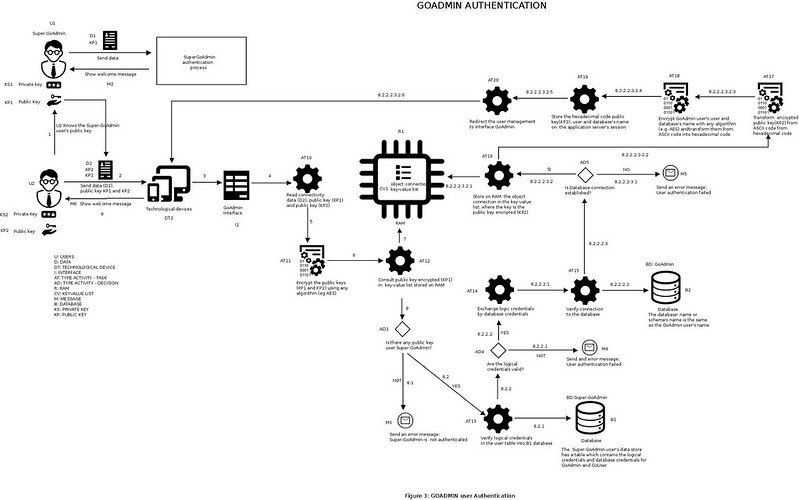
Figure 3 shows through a flow diagram, how the GOADMIN user (U2) is authenticated and opens a connection to database.
Once the user U1 is authenticated, communicates its public key (KP1) to the user U2. U2 sends the authentication data (data which are compared with the data stored in user table of Super-GoAdmin database (B1) and exchanged by connectivity data belonging to user U2), its public key (KP2) and U1's public key (KP1), using technological devices (DT2), which are connected to a network LAN or WAN , communicates with the application server, that contains the computing system which implements the GO AUTHENTICATION METHOD, this communication is done by an interface (I2), this interface allows to send the data (D2, KP1 and KP2), using the HTTP protocol, to application server, where the logic data (D2) are read, the public keys KP1 and KP2 are encrypted, the next step is to consult the encrypted public key KP1 in a key value list (CV1), which is stored on application server's RAM (R1).
If the encrypted key KP1 is not in the key value list (CV1) an error message (M3) is sent and shown through an interface because the user U1 is not previously authenticated. Otherwise, the logic credentials (D2) are verified with the data stored in the user table of Super-GoAdmin database (B1), using the object connectivity obtained by the encrypted public key (KP1).
If the logic credentials (D2) are not validated, an error message (M4) is sent and shown through an interface because U2’s authentication is incorrect. Otherwise, the connectivity data are obtained for GOADMIN user (U2) to verify the connectivity to its GoAdmin database (B2).
If U2 cannot establish with its database, an error message (M5) is sent and shown through an interface because of an error occurred in the authentication at database level. Otherwise, the objective connectivity belonging to U2 is stored in the key value list (CV1) which is stored on application server's RAM (R1) and the encrypted public key KP2 is transformed from ASCII code into hexadecimal code. Part of the connectivity data are the user and database's name, they are encrypted and transformed as was previously the KP2. The KP2, the user and database's name are stored on the application server's session and the user (U2) is redirected to GOADMIN's administration interface, giving a welcome greeting (M6).
GOUSER user Authentication(Zoom in)
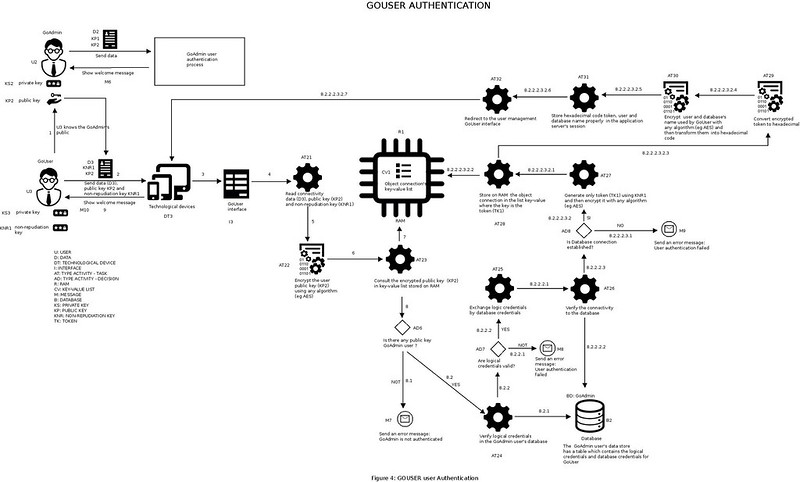
Figure 4 shows through a flow diagram, how the GOUSER user (U3) is authenticated and opens a connection to database.
Once the user U2 is authenticated, communicates its public key (KP2) to the user U3. U3 sends the authentication data (data which are compared with the data stored in user table of GoAdmin database (B2) and exchanged by connectivity data belonging to user U3), its non-repudiation key (KNR1) and U2's public key (KP2), using technological devices (DT3), which are connected to a network LAN or WAN , communicates with the application server, that contains the computing system which implements the GO AUTHENTICATION METHOD, this communication is done by an interface (I3), this interface allows to send the data (D3, KNR1 and KP2), using the HTTP protocol, to application server, where the logic data (D3) are read, the non-repudiation key KNR1 and public key KP2 are encrypted, the next step is to consult the encrypted public key KP2 in a key value list (CV1), which is stored on application server's RAM (R1).
If the encrypted key KP2 is not in the key value list (CV1) an error message (M7) is sent and shown through an interface, because the user U2 is not previously authenticated. Otherwise, the logic credentials (D3) are verified with the data stored in the user table of GoAdmin database (B2), using the object connectivity obtained by the encrypted public key (KP2).
If the logic credentials (D3) are not validated, an error message (M8) is sent and shown through an interface because U3’s authentication is incorrect. Otherwise, the connectivity data are obtained for GOUSER user (U3) to verify the connectivity to GoAdmin database (B2), where U3 has access to write and read.
If U3 cannot establish with B2 database, an error message (M9) is sent and shown through an interface because of an error occurred in the authentication at database level. Otherwise, a unique token (TK1) is generated using the KNR1, the objective connectivity belonging to U3 is stored in the key value list (CV1) which is stored on application server's RAM (R1) and the key is the token TK1, which is encrypted and transformed from ASCII code into hexadecimal code. Part of the connectivity data are the user and database's name used by GOUSER to establish a connection with B2 , they are encrypted and transformed as was previously the KNR1. The KNR1, the user and database's name are stored on the application server's session and the user (U3) is redirected to GOUSER's administration interface, giving a welcome greeting (M10).
Comentarios
Publicar un comentario